24 h with Huorong, a week with Comodo 12, a year with Bitdefender 2019 (or not)
While not being that much in the mood for writing, I had to clarify that I put a halt on my CCAV 2.0 journey. It worked well, but I wanted to try something else and… things escalated (sort of).
So here’s me, installing a Chinese AV! Um… how come, given that I definitely can’t stand Qihoo 360 (in spite of its rather useful HIPS notifications when a startup entry is added or sensitive Registry stuff is changed), and generally Chinese software is ugly and… well, first of all, ugly?
I found about Huorong Internet Security on a MalwareTips forum thread. (The download is here, but sometimes it may fail, or your DNS might not solve it; Google’s DNS is fine.) And the Chinese guy who presented it managed to persuade me that it’s worth trying it:
- Chinese and English (despite the website lacking an English version).
- “Best HIPS in the world.” Supports custom rules.
- Unlike Qihoo 360, this product catches Chinese adware and doesn’t whitelist them. (Crucial!)
- You can configure it to prompt you when a threat is found, rather than auto quarantining.
- Regular or High-speed (higher system load) scan mode.
- Own AV engine called Cobra (but Google translates it as Velvet). HVM (Huorong Virtual Machine): high capability of unpacking and detecting known threats/variants. Tiny virus database (below 5 MB) but covering most malware (one signature can match thousands of variants).
- Cons: Weak to new threats (no cloud engine yet); in some situations, performance is not so good.
I would add (on the positive side):
- Only 34 MB space once installed.
- Recognized by Microsoft as an antivirus software provider for Windows.
- Under “grayware” it can distinguish between adware, PUP/PUA, and “Kaspersky’s detected virus names starting with not-a-virus:” (which are not malware).
On the negative side, from my experience:
- Signature updates can be more than 24 hours old.
- Sometimes the update fails; try again and the update will most likely succeed.
- There is no way to temporarily disable the AV. Or even to disable it altogether! (That’s quite a deal-breaker.)
- On-demand folder scan is very slow (I didn’t check whether subsequent scans of the same files are faster).
OK then, I decided to just try it… alongside CCAV 2.0, as it didn’t complain about it, and the latter was light enough. Once Huorong installed, it will be the first one to detect a malware, and only then CCAV would have the chance to catch what Huorong missed (this is how their system hooks were chained).
I won’t describe much of anything, just click to enlarge the pictures below (they’re grouped in 6 galleries):
Gallery not found.
Quarantining needs to be configured in too many places, but the defaults are OK:
Gallery not found.
HIPS is fabulously strong (supposing it always works) and it covers pretty much everything one could think of!
Gallery not found.
The Toolbox is interesting (“Dianose” is only one of the many Chinglish labels):
Gallery not found.
There’s also a so-called System Diagnostics Toolkit, which helped me find something I didn’t know about the Kaspersky Anti-Ransomware Tool for Business and CCAV:
Gallery not found.
That is:
- CCAV adds quite a lot of system (ntdll.dll, kernel32.dll, KERNELBASE.dll, USER32.dll) hooks meant to allow sandboxing (CvavGuard32.dll!RunInSandbox) that intercept even the trusted binaries, which I find to be a waste and a potential performance issue.
- CCAV also “wraps” (intercepts) Kaspersky Anti-Ransomware Tool.
- Kaspersky Anti-Ransomware Tool stupidly intercepts even the Bluetooth service, Apache’s httpd, the VPN, Samsung Magician and other processes that couldn’t possibly perform any ransomware-related activity even if they wanted to… but CCAV also intercepted them (as a general AV, that’s justifiable for it).
In the end, Kaspersky’s Anti-Ransomware Tool was deemed useless and it was the first thing I uninstalled, even before Huorong.
But where does it stand detection-wise, our Chinese companion?
Funny thing, it was able to detect most of what I threw at it; for a useless figure, 94.2% of the very recent malware samples were detected on the spot!
Gallery not found.
The problem is with what it didn’t detect. At the time of the test, I selected 4 malware samples that were detected by many major vendors, and even by COMODO, but not by Huorong:
- https://www.virustotal.com/gui/file/0bb813c6e3ac571c067680f4ddb0365ab2140fc3d0903d12f3e3d0ef0ad837b5/detection
- https://www.virustotal.com/gui/file/44f8dbbfd7b51ad3267c3f80bbfb06ec2e47c8de7d61f740232c87e28cca5352/detection
- https://www.virustotal.com/gui/file/e899bdd1a3d186e2145a5173792510b1e0f7e65d52e3ed97681729ddd9765694/detection
- https://www.virustotal.com/gui/file/4824e6c823de77fc552c87536936ee59b320f908603e13581c88c4b7715545c9/detection
The fact that they were only 10-hr old on VirusTotal wasn’t a valid excuse. After all, COMODO is rated as having a rather poor detection rate (this seems to have changed lately), and yet it detected all of them…
…or did it? VirusTotal uses the “full” CIS/CAV/CW engine, not the cloud-only CCAV. And the problem is that 3 of the above 4 samples were only detected by the “full” Comodo, and not by Comodo Cloud AV!
Let’s put it this way, as I don’t know what it says:
In brief, Huorong Internet Security is small, light, powerful, with some limitations I could live with, but I can’t accept a detection rate that’s lower than COMODO’s!
Next stop, COMODO Antivirus, whose version 12 was just out of beta as I was testing Huorong!
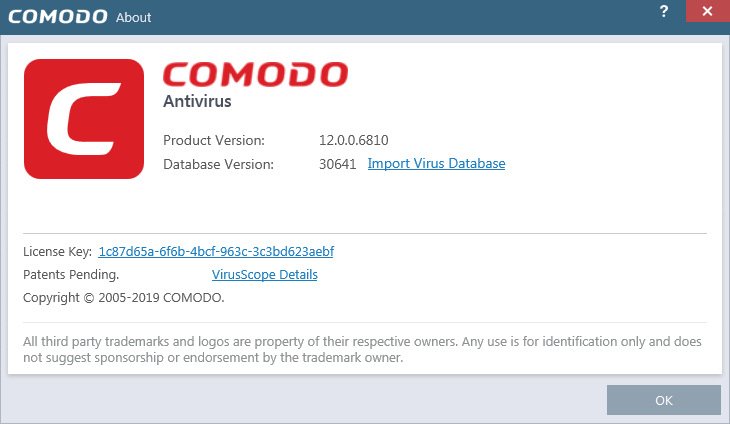
Despite the bugs reported in the beta stage, I found CAV 12.0.0.6810 (CAV, not CIS, which means it lacks the firewall, but not the HIPS) perfectly stable, well-behaved and unobtrusive (again, no firewall), even with the HIPS active! (This was tested under Win7 though; that planetary crap called Win10 might behave differently though.)
The good thing in CAV 12 over CAV 11 was that the sandboxing configuration got better, similar to what I had in CCAV 2.0 beta. But the best thing was what it offered me in comparison to CCAV (beyond the improved malware detection): unknown binaries weren’t automatically uploaded to Valkyrie! (Well, they still accumulated in a fucking list though, and I had to manually “trust” each of them, but that wasn’t a show-stopper of any kind.)
CAV 12 now has a quite large signature DB (it expands to about 435 MB), and it tends to be as prone to false positives as Avast and AVG, which is not great, but not critically bad either.
To make it short: Comodo AV 12 is now a very usable free product, at least on Win7, and to my surprise I now recommend it over CCAV 2.0 Beta (or non-beta, should it reach that level). The only nasty thing is that uninstalling it leaves too many traces (files, Registry keys).
One week later, CAV 12 still performed quite well, but there was an offer I couldn’t turn down: ComputerBILD 8/2019 offered, for only 4.50 € (the price of the CD edition; no need to pay more for the DVD), a 1-yr license for Bitdefender Internet Security 2019!
Yes, I know that there are countless reports of Bitdefender’s UI taking 600 MB of RAM, if not more. But on my system, it typically takes less than 60 MB, and never more than 200 MB during a scan. Most of the time the UI is not active, and bdagent.exe only takes 4…6 MB. I don’t know what “Windows 10 Guinea Pig Edition” are some people running, but my Win7 system is just fine with Bitdefender IS 2019!

This kind of licenses come in 6+6 months, meaning that 10 days prior to the expiration of the first 6-mo period, another 6-mo activation needs to be made; otherwise, the pleasant surprise is that adding this license preserved whatever was left from the 30-day trial license!
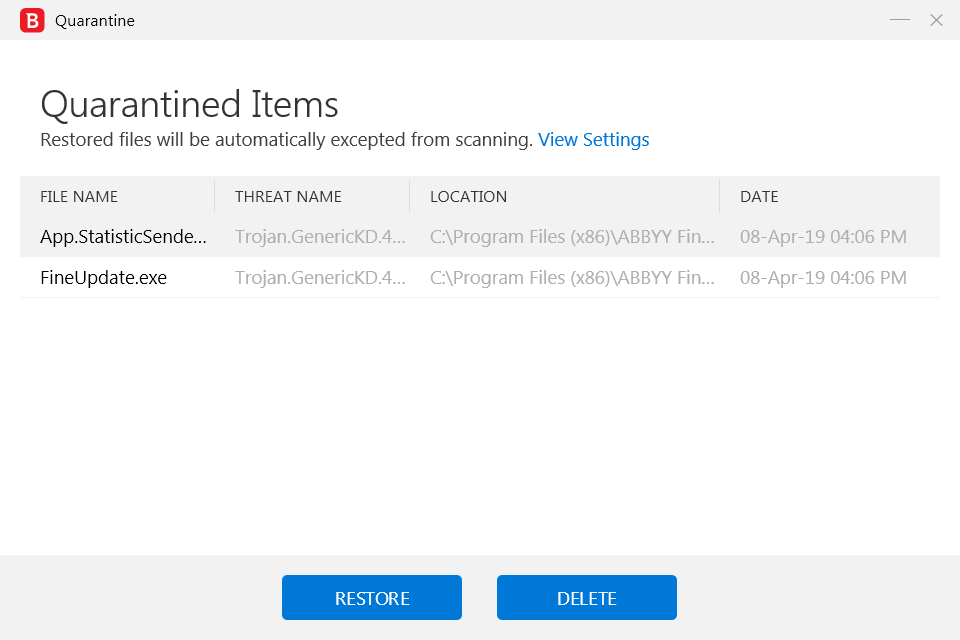
The reason I never liked Bitdefender was that it didn’t ask before doing whatever it thought appropriate with whatever it thought it was malware, even if told to ask first; things are now simpler: it just won’t ask, so the safe choice is to select the quarantining or the blocking:

Restoring from quarantine automatically whitelists, which is great:
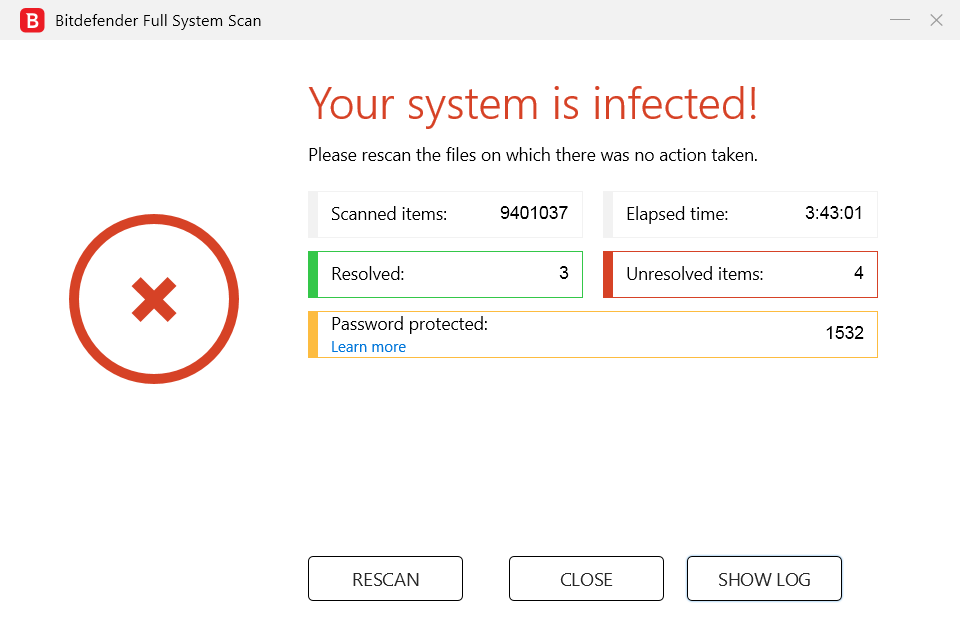
Even with the “unresolved” files added as exceptions, this idiot still cries “You’re infected!” after a system scan; BTW, scanning 9.4 M files took 3h43 on a SSD! (And the password protected count is wrong: only 51 files are password-protected archives; the other 1481 files are installers–most of which are stored by Windows under WinSXS and cannot be deleted–that could not be unpacked for analysis, but whose fault is that?)
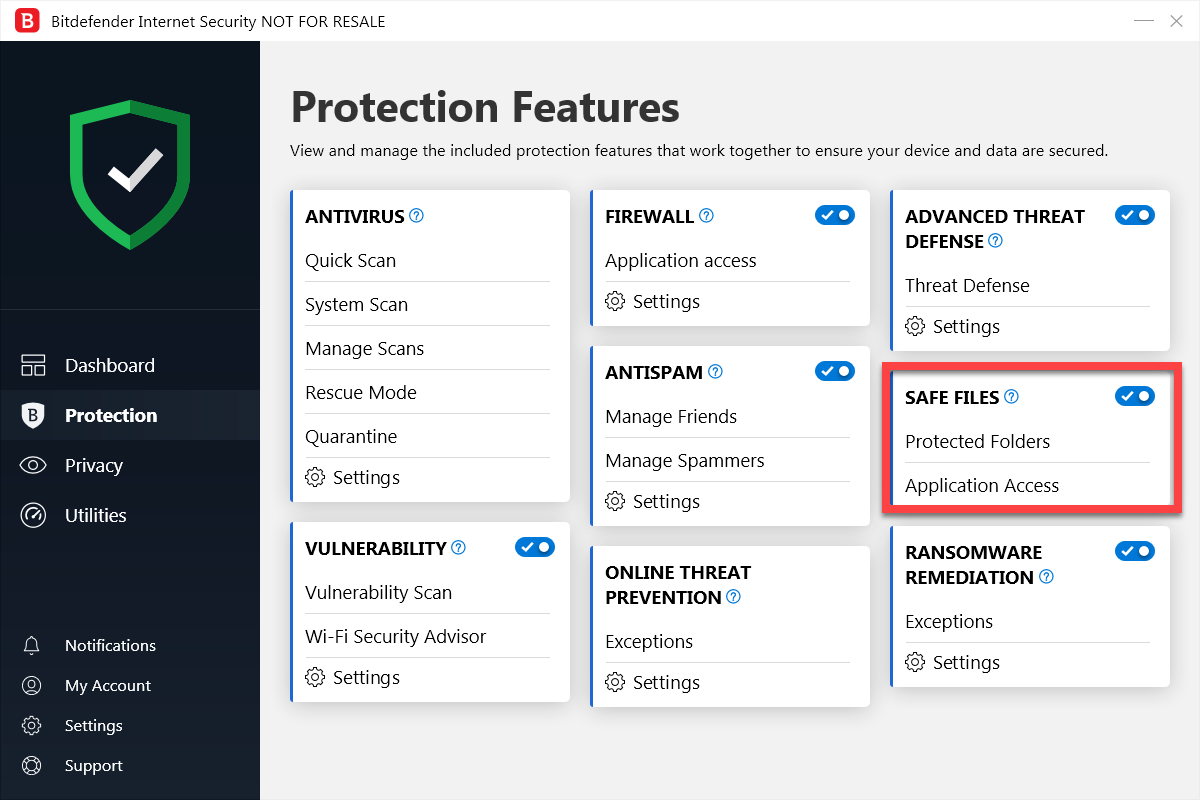
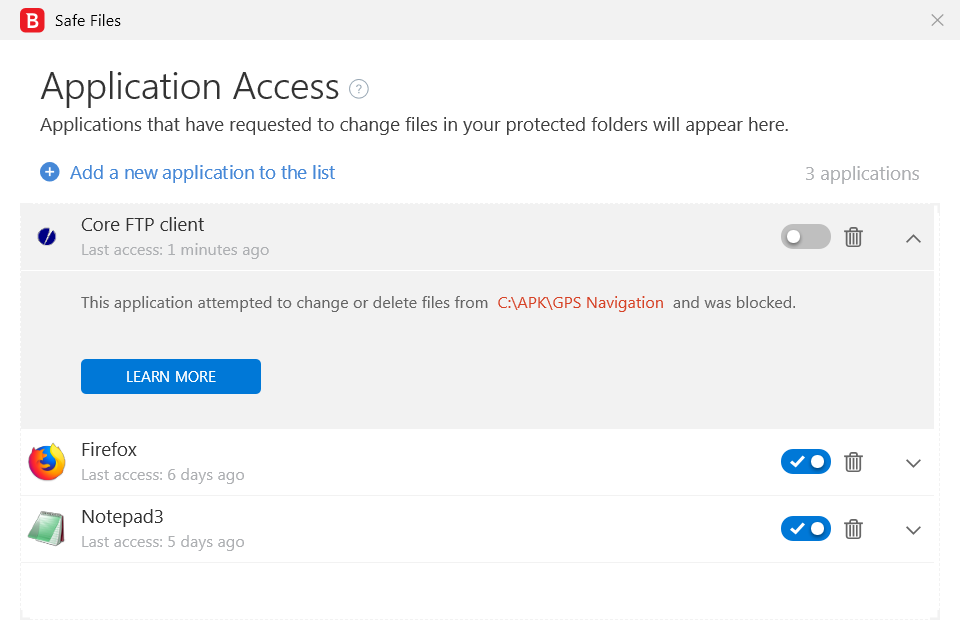
This annoyance aside, I very much appreciate its Safe Files feature: I had to whitelist Firefox and Notepad3 to even save files to a location listed under Protected Folders!
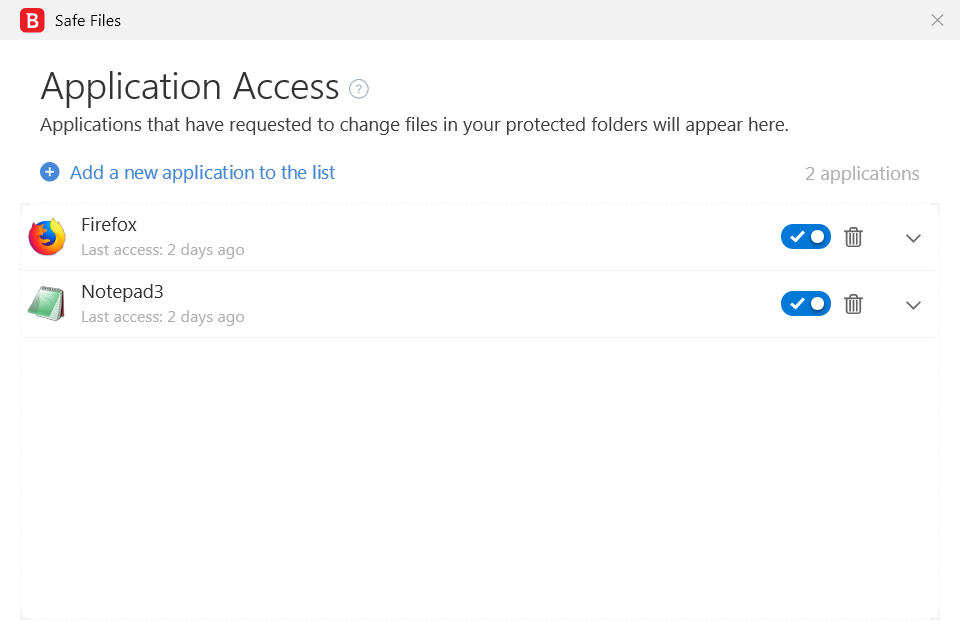
Programs that can change several files in a short time might need to be added as exceptions to Ransomware Remediation (which, strangely, is disabled by default):
Time will tell whether I’ll stick to Bitdefender IS until the end of the license or not.
UPDATE–The first glitch in Bitdefender 2019!
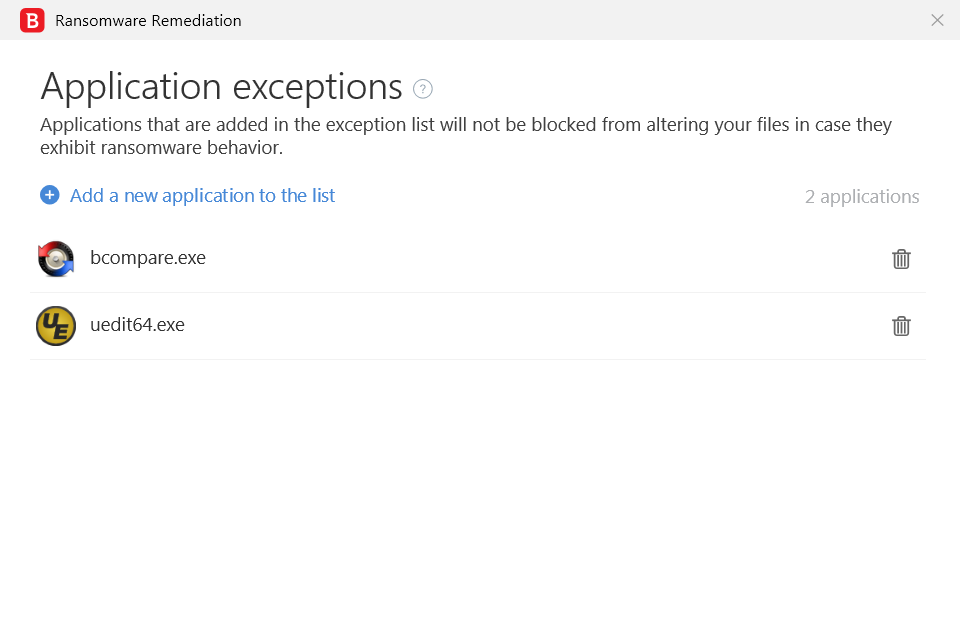
As I was deleting a local file from within CoreFTP, “Safe Files” popped up and informed me that “This application attempted to change or delete files from [a protected folder] and was blocked.” Well, unfortunately it was not blocked! Incidentally, CoreFTP deleted the file to the Recycle Bin, but it could have as well deleted it for good. It’s also irrelevant that this was a voluntary deletion–how could I trust Bitdefender that it would intercept a 0-day ransomware once it proved it sometimes cannot?
Only then I noticed that, despite the laudatory reviews everywhere, the most recent AV-TEST (Jan.-Feb. 2019) downgraded Bitdefender’s protection level from a perfect 6 to 5.5, simply because in February, the 0-day protection was only 98.8%:
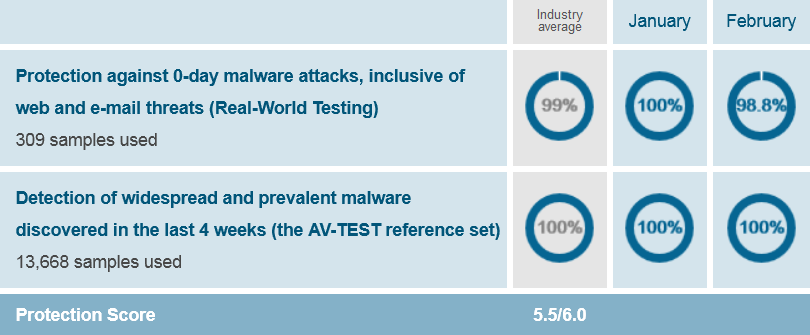
0-day malware… that’s exactly what Safe Files and Ransomware Remediation were supposed to help with! And I just experienced such a failure (thankfully, not from malware).
Apparently, after quite some time of perfect scores, Bitdefender lost 0.5 points everywhere:

To my surprise, Comodo (which once was credited by some reviewers with as low as 38% signature-based detections) has since more than one year a perfect protection score of 6:

That’s simply unbelievable. And yet, everyone is praising Bitdefender. OK, Bitdefender has fewer false positives, and very reassuring protection modules… except that I’m not trusting them anymore!
I guess I’ll try to squeeze some more value from the 4.50 € I paid for the license (the magazine also included a 1-yr LanguageTool Premium license, really a 59 € value, but originally I purchased it for Bitdefender). Or maybe not.

Dump all/any of your antivirus software and go back to Linux 🙂
Nice to see that you are blogging again.
I can even live without an AV, but I like to play the game and pretend I need one 😀
Oh, an almost uknown chinese product ? I would never have had the courage to try that. 🙂
So, now, Bitdefender… Finally. I told you that you had to try it again 😛
Just, maybe you should try/use the Dark Mode… 😉
There is no dark theme in Bitdefender. At least, not under Win7. Oh, not only here…
“Bitdefender has adopted white theme in 2019 version.” https://www.dealarious.com/blog/bitdefender-total-security-review/
“The dark theme is gone, and there’s a new centralized Dashboard.” https://www.pcworld.com/article/3296003/bitdefender-total-security-2019-av-review.html
This last guy is stupid enough not to understand the utility of the Safe Files feature:
Wow, how difficult it is to whitelist a few programs!
This is strange when everything goes to dark… 😉
The question I’m most interested in: is Windows Defender enough for day to day protection, if you are careful not to visit nefarious sites or download dubious stuff?
For most people and under Win10, yes. (No torrents, cracks, etc.)
I just found a failure in Bitdefender 2019! (Update at the end of the post.) This endangers my sticking to this product. I’ll have to think about it.
I’ve just uninstalled Bitdefender 2019. It lasted on my laptop only 10 days.
Beyond the discovered failure into protecting the “Safe Files” (which should be a deal-breaker in itself), I noticed that it developed a slowness that affected the launching of just about any program. As long as I wasn’t launching a new binary, unknown to it, it was totally unacceptable to have its launching delayed by 2-3 seconds EVERY SINGLE TIME.
Usually a reboot mitigated the issue, but I don’t want to reboot my laptop for the sake of an antivirus! Either way, this made me suspect it was mismanaging the system handles (see the Performance tab in the Task Manager). In my Win7, a fresh reboot with NO SECURITY product whatsoever gives the number of used handles of about 20k. During usage, handles raise to 30-36k with NO SECURITY product (and Windows Defender disabled as a system policy), but with Bitdefender, handles were reaching 60k. I suspect this was the reason of the slowdown.
Now I have to decide what to use instead.
■ I just tested TrendMicro Antivirus+ 16 Beta, and it was slower than version 15.
■ I also tried Ahnlab V3 Lite, now in English and free (see here and here). There are several things I didn’t like.
■ I should probably go back to KSC Free, but on my wife’s laptop, Kaspersky just showed signs that it “forgot” about a couple of exceptions. I have to investigate the issue.
■ Comodo 12 (CAV or the full CIS?) is usable, I could go back to it, but I’m so bored…
■ On the other hand, CCAV 2 beta, albeit much smaller and lighter than CAV/CIS, has a lower detection rate, and it automatically uploads the unknown binaries to Valkyrie (OK, this can be disabled). Both issues are quite annoying. (No HIPS either, but the sandbox works.) Oh, and this beta has never been officially announced in Comodo’s forums; is CCAV neglected lately? Is CCAV going to be abandoned?
Quelles merdes tous ces produits !
F-Secure, Panda, Nod32… ? Sinon, Linux. C’est gratuit et ne nécessite aucune de ces apps. Sinon, macOS.
Au sujet de Kaspersky, j’ai ici aussi le même genre de comportement avec une app. Une seule. Toujours deux messages qui apparaissent malgré que je lui dit toujours qu’elle est « de confiance » et en liste blanche…
Kaspersky: indeed, it’s about those two successive warnings.
F-Secure seems to have been switched from Bitdefender to Avira’s signatures. Panda is not doing well lately. ESET NOD32 didn’t convinced me when I ran it for about 9 months (another free ComputerBILD license).
In a recent (April 11, 2019) update of his review of Comodo Antivirus, Neil J. Rubenking doesn’t say whether he tested version 11 or 12 (the URL still refers to 10), and his partiality can be seen e.g. in the fact that he purposely mixes (1) the fact that only one of the five tweaked ransomware samples ran in the sandbox and (2) the fact that the rest of them obviously encrypted whatever they found. The phrasing below suggests that even the contained ransomware managed to do its job… or maybe only “one component” of one ransomware sample was automatically contained, which means that ALL ransomware samples were NOT sandboxed?!
As usual, NJR is unfair; and he doesn’t seem to understand Comodo’s sandboxing (not to mention how it can be tweaked). I’m going back to CAV 12.
> on my wife’s laptop, Kaspersky just showed signs that it “forgot” about a couple of exceptions. I have to investigate the issue.
If you find the solution, I take.
Vous êtes preneur, vous dites? But I don’t investigate anymore, I’m tired of all such crap.
Back to CCAV 2 Beta, with custom settings. After all, the best protection is when an unknown file, even if not identified as malware, is blocked or sandboxed because it’s neither signed by a trusted vendor, nor vetted by Comodo’s Valkyrie. And the sandbox can be configured to be more restrictive: no network, no real access even to the Download folder (normally allowed by Comodo). When I add a binary to Trusted, I must know what I’m doing.
But I don’t need other crap that slows down my system. And no, I’ll never sandbox any browser, they’re all (Firefox, Chrome) pretty crappy as they are.
CCAV is the only AV that’s so light that it’s almost as I had no security solution at all (Panda not considered… because I don’t like it anymore); I know how it feels when even WD is disabled (by Group Policy) and trust me, NO ANTIVIRUS is light enough to match that feeling. But CCAV 2 Beta is the closest I could get, especially if I’m careful to configure it properly.
> NO ANTIVIRUS is light enough to match that feeling
Even something like Webroot ?
Webroot, indeed. I was forgetting it. It’s a sort of a maverick, and I don’t know what to think of it: its detection rate cannot be accurately estimated, as many of the detections only happens when one tries to run those binaries.
Remember how I discovered that Bitdefender only claimed to have blocked CoreFTP from deleting a file from a protected folder? Here’s how a real ransomware managed to screw 3 files despite BitDefender having claimed to intercept it: www.youtube.com/watch?v=wrlgnt_HLlY
Pathetic. It was supposed to protect such a folder from ANY unauthorized access! Even to have Firefox SAVE files in such a folder needs you to whitelist it, and here’s how an unknown binary manages to do almost whatever it wants. More than pathetic.
Just for the record: I switched to AVG Free. Rationale:
■ AVG and Avast are light enough and they catch most malware; they also have a Behavior Shield.
■ While Avast and AVG are now using the same engine and only different GUIs, I prefer AVG’s GUI, which in the free edition seems less cluttered. It’s worth noting that Avast has more editions than AVG (Avast IS @60 €/yr, Premier @70 €/yr and Ultimate @120 €/yr vs AVG IS @60 €/yr and a less powerful Ultimate @80 €/yr which isn’t even available everywhere), but all I need is the free edition.
■ As Mike Williams notes here, AVG Free doesn’t require any account in order to work (Kaspersky does for both KFA and KSC Free).
■ I like AVG’s comparative lack of extra (read: unneeded) features, and I’ve actually only installed the “Computer” module, without “Web and E-mail”. To quote the same guy: «Unlike Avast, AVG AntiVirus Free doesn’t use a browser extension as a first line of internet defense, which means dangerous URLs aren’t highlighted in your search results. The core antivirus engine still detects and blocks web threats, though, and will also scan any downloads you make, so you’re still well protected.»
■ This is exactly what I want: to have the downloaded file scanned. I DON’T WANT to have any URL blocked! Let me visit whatever fucking URL I want! It’s my fucking computer and my fucking browser. (Besides, generally entire websites are blocked, not just a file or a page on a site.)
■ Same Mike Williams from TechRadar notes about AVG Free: «Avast has same engine but more features.» The day before, while reviewing Avast Free: «Uses many tricks to try to sell other Avast products.» So AVG is a better choice!
■ No, it’s not that intrusive and nagging anymore. Under Settings, General, Personal Privacy, uncheck all the boxes and you’re done.
■ Just like Avast, AVG is very configurable, and it also has a hardened mode (but without the choice between Moderate and Aggressive) which relies on Avast’s file reputation service.
■ The major drawback: everyone is only talking about Avast, even if AVG is basically the same product with a different UI! AVG’s forum is not quite a forum, but Avast’s forum only mentions AVG’s beta releases, and very few people comment on AVG there (or anywhere else for that matter). OK, maybe I have a tendency to go against the flow; I’m pretty sure AVG is going to die eventually and Avast will take over completely, but as long as AVG still exists…
■ BTW, I switched to the latest beta, and it’s very stable on Win7.
■ Setup stubs for beta versions:
AVG: http://public.avast.com/mkt/betaav/avg_free_antivirus_setup_online.exe
Avast: http://public.avast.com/mkt/betaav/avast_free_antivirus_setup_online.exe
■ Setup stubs for final versions:
AVG: https://bits.avcdn.net/productfamily_ANTIVIRUS/insttype_FREE/platform_WIN_AVG/installertype_ONLINE/build_RELEASE
Avast: https://bits.avcdn.net/insttype_FREE
■ Full setups for final versions:
AVG: https://bits.avcdn.net/productfamily_ANTIVIRUS/insttype_FREE/platform_WIN_AVG/installertype_FULL/build_RELEASE
Avast: http://files.avast.com/iavs9x/avast_free_antivirus_setup_offline.exe
■ The versioning is confusing between the two products, meaning that VERSION and BUILD are different, and the versions are not the same for AVG and Avast, even for the same build, e.g.:
AVG version 19.5.3092 (build 19.5.4431)
Avast version 19.5.2377 (build 19.5.4431)
■ I forgot to add why Free is enough for me: I don’t require anymore a specific Anti-Ransomware module based on Protected Folders, as I’ve seen how this feature simply doesn’t work in Bitdefender (see my previous comment); it works in Trend Micro, but Trend is heavy; and Kaspersky simply doesn’t have this kind of Protected Folders at all!
What I added to AVG Free: Windows Firewall Control, originally by BiniSoft, now in MalwareBytes’ portfolio (but totally free). It allows for an easy customization of Windows Firewall. If you want, you can create a rule to block AVG’s overseer.exe (which is Avast’s overseer.exe) to phone back home 🙂 It actually starts in the default “Low Filtering” (orange) mode, where outbound connections that do not match a rule are allowed, just as it was before installing it. By switching to “Medium Filtering” (green), outbound connections that do not match a rule are blocked; something more like Comodo Firewall, huh?
All anti viruses are bull crap, I hate them with a passion, I just use Local Security Policy in Windows Ten, whitelisting my trusted apps and folders, the rest of the system is under “lock down” all the time, no worries about anti viruses doing something funny with the OS, no accounts to create, no trial versions to test, everything is so peaceful and the performance is not bogged down by useless “protection” software, of course I do scan the system from time to time with Emsisoft Anti Malware (Malwarebytes is shite), guess what, my computer is always clean and pristine, without the headache you have with antiviri (the only headache is configuring for the first time secpol.msc)!
A severe case of comma splice.
Daca stau si ma gandesc, n-are nici o treaba cu ortografia engleza, pur si simplu am uitat cratimele, scuze!
Care cratime, frate? Nu pui spațiu după fiecare virgulă (am adăugat eu) și înlănțui prea multe propoziții separate doar de virgulă (de-aia e vorba de „comma splice” și nu de „run-on sentences”). În rest, nu sunt greșeli.
I just noticed that AVG hasn’t released any signatures for 18 hours! Checking reveals that the last version 190527-4 was released on May 27 at 5:40 PM, and we’re on May 28, 11:30 AM.
Unless they neglected AVG, I suppose this is valid for Avast too.
I don’t find it acceptable.
EDIT: Update 190528-6 was released at 12:51 PM, some 19 hours and 11 minutes after the previous one!
That was fucking too much. Can’t one have a SIMPLE antivirus that doesn’t want to stick its nose into everyone’s ass and that DOES NOT AUTOMATICALLY UPLOAD FILES for analysis?
I need to find a replacement to this shit.
That was the last straw! I’d rather use a homeopathic antivirus than this kind of crap!
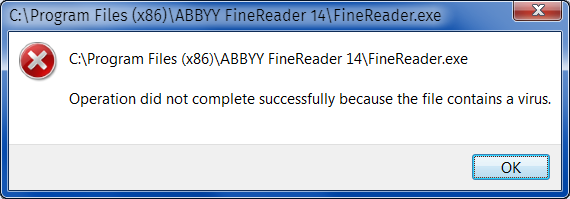
– The binary was already added as an exception.
– The real-time protection was disabled.
– Windows Defender is disabled by policy.
And yet…
It’s not the first time a security product does this on me; but this time I am really tired of such shit.
In 26 years of using DOS and Windows, I never got infected, and it wasn’t because an antivirus prevented it. Now I just need an unobtrusive AV that keeps Windows happy that it’s there but doesn’t do much; for the rest, there is common sense, then VirusTotal…
As Windows Defender (MSE in Win7) is heavy, and most other products are trying to do too much, the quest for a really light free product seems an impossible task already.
Back to something reasonable:
 HINT: To install KFA 2020 Beta out of the (stub) KIS or KTS installer, use this command line:
HINT: To install KFA 2020 Beta out of the (stub) KIS or KTS installer, use this command line:
startup.exe /pPRODUCTTYPE=kfaAll’s well when it’s all green:

Current solution (light! light! light and non-intrusive!):
1. Windows Firewall Control set to Medium Filtering (green). A must-have. Any attempt to even an outbound connection must be approved (on Medium Filtering).
2. 360 TSE, even if it’s Chinese and even if the “small” TSE is kept at version 8.8.0.xxxx, while the “full” TS is at 10.6.0.xxxx.
IMPORTANT!
— NO Avira or Bitdefender signatures, but only its own Cloud and QVM engines. This way, it’s really light (with 3rd-party engines it becomes heavy; and both Avira and Bitdefender signatures are less effective in 3rd-party products).
— Internet Protection disabled: I want to be able to visit whatever I want and to download whatever I please. Only then I want to get any files scanned.
— Believe it or not, Qihoo 360 has great heuristics, especially when it comes to scripts of all kinds (the primary source of ransomware). I have tested it thoroughly with REAL MALWARE (not false detections of keygens and stuff) and it detected them all! Moreover, if I tell it to ask first, then this is what it does.
— Unlike most other products, 360 also informs me of (attempted) changes in areas of the Registry (including Run, RunOnce, services, tasks) which I want to be able to control even against some legitimate installers.
— To avoid the nagging, I use Windows Firewall Control to block the outbound connections of “C:\Program Files (x86)\360\Total Security\PromoUtil.exe”. Easy-peasy.
— Oh, it has a Sandbox, just in case.
EDIT: Switched from 360 TSE to KSC 2020 Free (more configurable than KFA 2020):
Sorry to disappoint, but I switched again, this time to ESET NOD32:
I already had an experience with ESET 3 years ago.
Reason #1: all things considered, ESET is the lightest of all.
Reason #2: on eBay one can find ESD licenses for $2.49…$2.99/yr per PC, both for NOD32 Antivirus and NOD32 Internet Security. I preferred the AV for simplicity (it still has Internet Protection, and without an add-on, which makes it better than Kaspersky).
I spent $2.59 for a 1-PC 1-yr license that could activate either of IS and AV, and I activated the AV edition. I don’t need unnecessary shit.
The only thing with NOD32: the HIPS should be configured properly for an increased protection against unknown exploits (the default is just too weak). I suggest the Learning Mode for a week, followed by “Ask user”. The Interactive Mode is tempting, but it’s more annoying than Comodo! (It would even bother the user with “firefox.exe tries to launch firefox.exe”!)
My wife stays with KSC Free, she doesn’t like to be bothered with fine-tuning AV software.
P.S.: Why I uninstalled Qihoo 360 TSE? Because it silently blocks the customization of the Notification Area Icons by changing
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\NoAutoTrayNotifyfrom 0 to 1.